Working through Pritunl 1.32 API changes…
I stood up the infrastructure for an upgraded Pritunl Proof-of-Concept (POC) with a Mongodb Atlas database backend using Terraform. The next steps for the POC were split. The team responsible for managing OKTA would configure SAML 2.0 authentication, and I would sort out configuring Pritunl organizations, users, servers and routes via Terraform.
The POC runs the latest version at the time of writing, v1.32.4278.46 3b595f. When I began exploring the API integration, API keys, tokens and secrets, I found much of the functionality - including access to the API and SAML configuration - is gated behind the Enterprise license.
To proceed, I needed to retrieve the existing Pritunl enterprise key from our production Pritunl service.
The production install of Pritunl runs on an AWS ECS cluster backed by EC2 instances. I used the .pem SSH key, logged in to one of the EC2 instances backing the cluster, and accessed the Docker container with:
| |
Once I applied the Enterprise license key, SAML configuration became available immediately. The API panel under the admin users was not available.
Installing the Enterprise license in Pritunl does not immediately enable the API access checkbox or reveal the API token and secret in the admin UI. In the Pritunl formus, Admins have reported that after applying the license, the API panel remains hidden until the server is restarted or the service is reloaded.
Nothing in the forum indicates a delay due to caching or time — the consensus is that a proper restart of the Pritunl process/service is required for the UI to reflect the license change (the license enables the feature, but the UI only exposes it after restart)
So to trigger the API panel UI:
- Apply the Enterprise license (e.g., via docker exec … pritunl set app.license …).
- Restart the Pritunl server/service or container.
- Then visit Admin → Users again, and the API toggle plus generated token/secret fields will appear in the admin user settings.
API Auth: Session vs HMAC
Once the Enterprise key is loaded into Pritunl, in the settings for an admin user is a checkbox allowing API authentication, and the token and secret are visible.
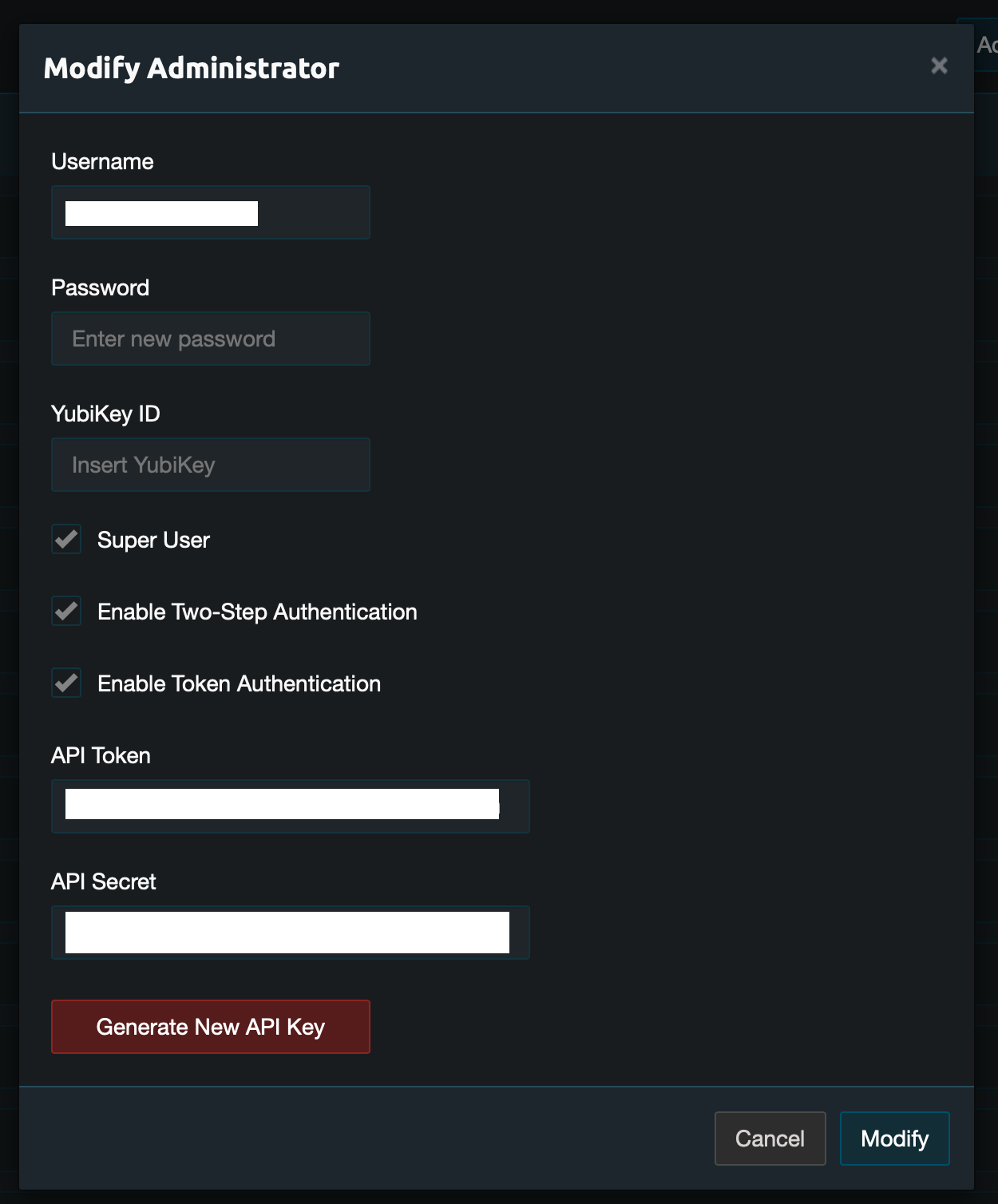
When I initially applied the Enterprise license without restarting Pritunl, the API panel under admin users seemed to be missing. I started exploring how authentication worked against the API and looked at scripting a method to interact with the API with the assumption that that panel was now gone from Pritunl. Note: that’s actually not the case, the panel is visible in the UI under admin user settings after the Pritunl service is restarted.
Failed Approach: Session Cookie Auth
My first attempt at scripting API access used browser-style session authentication. The Go script logged in, received a session cookie, and attempted to make authenticated requests using the cookie. It failed consistently with 401 Unauthorized.
| |
That result proved session cookie auth was not going to work.
Working Approach: HMAC Auth in Go
From zach (creator of Pritunl).
| |
That thread points to this python code , which implements HMAC-based API authentication using a custom signature scheme.
After studying the Python code, I asked ChatGPT to help rewrite my Go script using the HMAC signature pattern. The resulting script calculates the signature from:
- The token
- A Unix timestamp
- A random nonce
- The HTTP method and path
Then it sends the request with four headers: Auth-Token, Auth-Timestamp, Auth-Nonce, and Auth-Signature.
The script pulls these values from CLI flags, environment variables, or AWS Secrets Manager and uses them to query the Pritunl API.
This script:
| |
…was able to authenticate and create a json representation of the Pritunl configuration.
Terraform Compatibility
This Pritunl Terraform module , specifically this line of code. :
| |
show that this module should work using the token and secret as auth. The line suggests that the provider does implement HMAC-based request signing, albeit using MD5 as the hash function (which is surprising — Pritunl’s current code uses HMAC-SHA256). This may indicate either compatibility with older versions or a custom implementation.
Getting the API Token and Secret
I found you could see the admin user token adn secret directly in the mongodb database, even if the Pritunl API did not expose it. I believe it is actually present under the hood, and then the Enterprise key makes it visible in the UI, but I have not confirmed that to be the case.
You log into the mongodb database using mongosh:
| |
Query the administrators collection:
| |
Look for:
| |
From here, you use the token value as the api token, the secret value as the api secret, and if auth_api is true, the go code above will run through the internal config and assemble it as a json object.
Terraform
With the token and secret retrieved from MongoDB, and a working HMAC authentication implementation validated in Go, the next step is testing whether the Terraform provider can authenticate and apply changes using the same credentials.
Verified - the disc/pritunl module does work with those embedded API token and secret strings.
It turns out the OKTA SAML 2.0 integration we’ve configured creates and populates users on the fly. We won’t use terraform at all for users, and only for servers and organizations and routes. At this point the initial POC is done.
—doug